
SysAlbania
CyberSecurity
This repository contains the best books for both bug hunters and people studying cybersecurity.
Articles by SysAlbania
16 articles published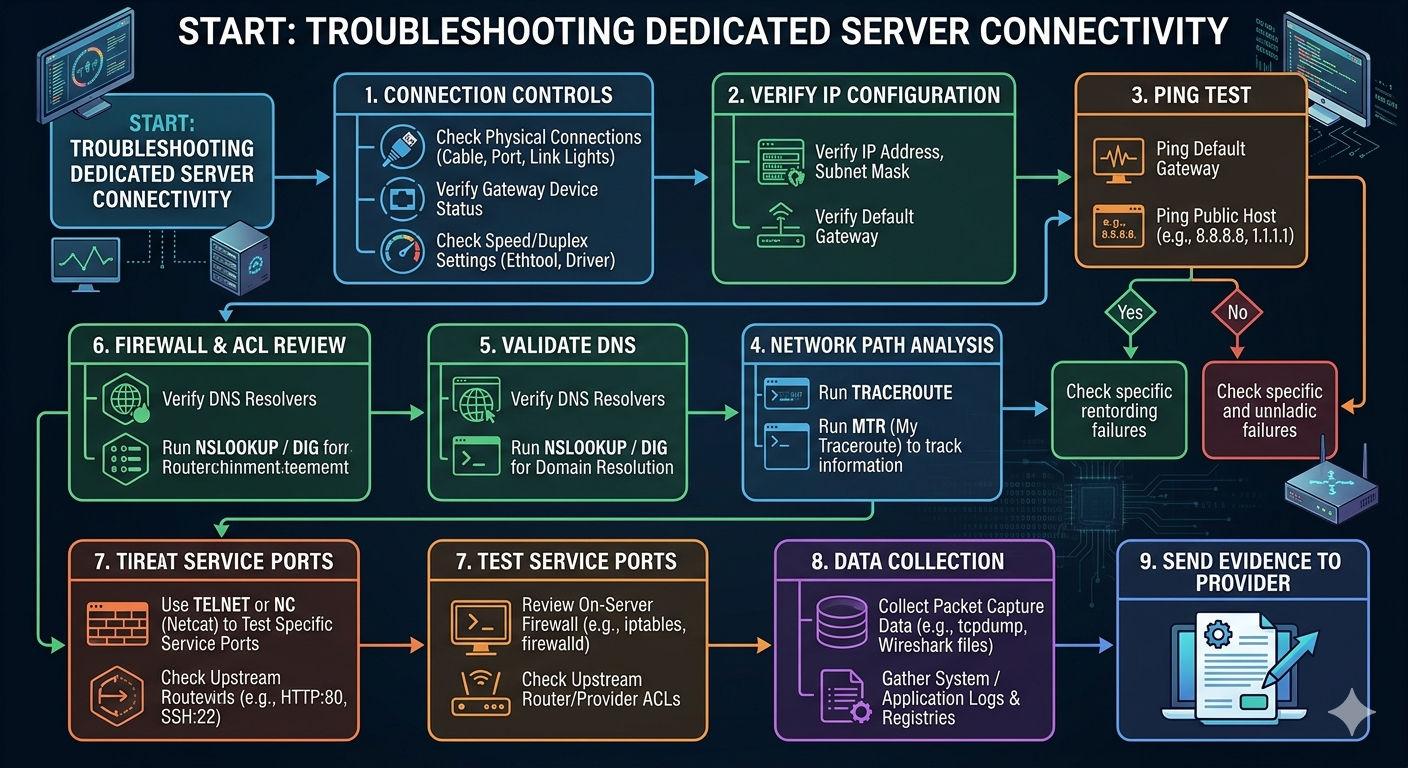
How to solve network connectivity problems on dedicated servers
To solve network connectivity problems on dedicated servers, start with connection controls (cable, gateway, speed/dupleks), verify IP/snut/gateway, make gateway ping and public hosts, run traceroute/MTR for tracking information, validate. DNS, review firewall/ACL rules, test specific service ports, and collect package capture data/registrees before sending the evidence to your provider.

What Is Penetration Testing
Penetration testing (pen testing) is a legal and authorized simulated cyber-attack on a computer system to evaluate its security. Pen testers act like real hackers: they use the same tools, techniques, and thinking to find and show weaknesses that could hurt the business.

What is Vulnerability Assessment
A vulnerability assessment is the process of checking a system to find security weaknesses. The goal is to know whether a system can be attacked, how dangerous the weakness is, and how to fix it.

Understanding Android Mobile Architecture and Its Security Vulnerabilities
Android is one of the most widely–used mobile operating systems in the world. To run smoothly on millions of devices, Android is built using a layered architecture. Each layer has a specific function that allows applications, system services, and hardware to work together.

Understanding what Threat, Vulnerability, Risk, Impact, Severity, and assesing Severity based on CVSS
A threat is anything that has the potential to do damage, even if the damage has not happened yet. In this case, a thief who walks around looking for houses to break into is the threat. The thief might or might not attack, but the possibility exists, and that possibility itself is the threat.

Understanding What IP, Port, and Protocol Is
This topic focuses on understanding the definitions of IP addresses, ports, and protocols, the differences between each of them, as well as commonly used standard ports and the network services that operate on those ports.

Active Information Gathering in Cybersecurity
In cybersecurity, the first phase of ethical hacking is called Reconnaissance or Information Gathering. This phase focuses on collecting information about a target before attempting any attack or security testing. Information gathering is divided into two main types: Passive Information Gathering Active Information Gathering

Captcha Bypass
Do not send the parameter related to the captcha. Check if the value of the captcha is in the source code of the page. Change some specific characters of the captcha parameter and see if it is possible to. When a new Captcha code is created, the previous code will expire.

Network Mapping for Beginners: Exploring Networks with Nmap
Network mapping is an early stage in network analysis, cybersecurity, and penetration testing activities. At this stage, the main objective is not to exploit vulnerabilities, but to understand the structure of the network. We want to know what devices exist, which hosts are active, and how the network is organized.